AEREDIUM
Technical White Paper
A Multi-Cloud Layer 1 with Hardware-Verified Execution
and Quantum-Resistant Attestation
Key Features
- TEE-Based MEV Protection: Hardware isolation prevents validators from seeing mempool—eliminating front-running and sandwich attacks
- Full EVM Compatibility: Standard ECDSA signatures, standard addresses, standard tooling (MetaMask, Hardhat, Foundry)
- Quantum-Resistant Attestation: ZK-STARKs for execution proofs (hash-based, no trusted setup, resistant to quantum attacks)
- Multi-Cloud Architecture: Validators distributed across AWS Nitro, Azure SEV-SNP, and GCP Confidential Space
- Bitcoin Anchoring: Immutable attestation records anchored to Bitcoin for independent verification
Table of Contents
1. Executive Summary
AEREDIUM introduces a new category of blockchain: the TEE-Attested Blockchain. This architecture achieves MEV protection through hardware isolation while maintaining full EVM compatibility and practical performance. Quantum resistance is implemented at the attestation layer using ZK-STARKs, protecting the integrity of execution proofs without impacting user transaction throughput.
The architecture works as follows:
- Clients submit standard EVM transactions using ECDSA signatures
- Transactions enter the mempool inside hardware-isolated TEE validators where they are invisible to operators
- Validators reach consensus using TEE-BFT
- Each validator executes transactions within its TEE
- Execution is attested using ZK-STARKs providing quantum-resistant proofs without trusted setup
- Attestation proofs are periodically anchored to Bitcoin
How TEE Isolation Achieves MEV Protection
- Validators run inside hardware-isolated TEEs (AWS Nitro, Azure SEV-SNP, GCP Confidential Space)
- TEE isolation means validator operators cannot see mempool contents
- If operators cannot see transactions, they cannot front-run, sandwich, or reorder for profit
- Hardware provides the isolation—no encryption overhead required
- Standard EVM transactions flow through; only the execution environment is protected
Decentralization by Technical Design
- No manual transaction ordering — TEE-BFT determines order programmatically
- No operator access to execution — TEE isolation is hardware-enforced
- No code modification — attestation proves exact approved code is running
- No single cloud dominance — multi-cloud architecture with enforced diversity
- No human intervention possible in consensus, execution, or attestation
AEREDIUM achieves true decentralization through technical architecture, not policy. Validators operate autonomously within hardware-isolated TEEs with no human intervention possible in transaction ordering, execution, or attestation. The protocol—not people—enforces the rules.
1.1 The TEE-Attested Blockchain Category
Blockchain infrastructure has evolved through distinct categories:
| Category | Examples | Trust Model |
|---|---|---|
| Public L1 | Ethereum, Solana, Avalanche | Cryptographic proofs; anonymous operators; MEV vulnerable |
| Permissioned | Hyperledger, R3 Corda | Known operators; centralized control |
| L2 Scaling | Lightning, Arbitrum, Optimism | Inherit L1 consensus; execution/scaling layer |
| TEE-Attested | AEREDIUM | TEE isolation + ZK-STARK attestation + Bitcoin anchoring |
1.2 The Problem
Current blockchain infrastructure faces fundamental challenges:
- MEV Extraction: In 2024, over $1.4 billion was extracted from users through front-running, sandwich attacks, and transaction reordering.
- Execution Accountability: Traditional blockchains cannot prove what code validators ran or whether execution environments were compromised.
- Future Quantum Threats: Current ECDSA signatures will eventually be vulnerable to quantum computers.
- Institutional Requirements: Enterprises require SOC 2 compliance, audit trails, SLAs, and accountable operators.
1.3 The Solution
- TEE-Isolated Execution: Validators operate within hardware-isolated TEEs. Operators cannot access mempool, view pending transactions, or modify execution.
- Standard EVM Compatibility: User transactions use standard ECDSA signatures (secp256k1). Full compatibility with MetaMask, Hardhat, Foundry.
- ZK-STARK Attestation Layer: Execution proofs are generated using ZK-STARKs—quantum-resistant, no trusted setup required.
- Multi-Cloud Deployment: Validators distributed across AWS Nitro Enclaves, Azure SEV-SNP, and GCP Confidential Space.
- Bitcoin Anchoring: ZK-STARK attestation proofs anchored to Bitcoin every 100 blocks.
1.4 Key Differentiators
- Hardware-Based MEV Protection: TEE isolation prevents validator operators from seeing mempool—no encryption required, no performance overhead.
- Full EVM Compatibility: Standard ECDSA transactions, standard addresses, standard tooling. Deploy existing Solidity contracts unchanged.
- Quantum-Resistant Attestation: ZK-STARKs use hash-based cryptography resistant to quantum attacks. No trusted setup ceremony required.
- Efficient Proof Batching: One ZK-STARK proof (40-50KB) can attest to thousands of transactions.
- No Client-Side Changes: Users interact with standard wallets. No special client software.
- Institutional Compliance: SOC 2, ISO 27001, and FedRAMP-ready infrastructure with known, accountable operators.
1.5 Cryptographic Architecture
| Layer | Algorithm | Size | Purpose |
|---|---|---|---|
| User Transactions | ECDSA (secp256k1) | 65 bytes sig | EVM compatibility, standard wallets |
| Execution Attestation | ZK-STARK | 40-50 KB/block | Quantum-resistant proofs |
| State Verification | Merkle Proofs | Variable | Standard blockchain verification |
| Bitcoin Anchoring | SHA-256 | 32 bytes | Immutable commitment |
1.6 Performance Characteristics
| Metric | Traditional BFT | TEE-Enhanced BFT |
|---|---|---|
| Minimum validators for f faults | 3f + 1 | 2f + 1 |
| Commit rounds | 3 | 2 |
| Finality (typical) | 3-6 seconds | 1-2 seconds |
| Transaction format | Standard EVM | Standard EVM |
2. Market Context
2.1 The MEV Crisis
Maximal Extractable Value (MEV) represents profits from manipulating transaction ordering:
| MEV Metric | Value |
|---|---|
| Total MEV extracted (2024) | $1.4+ billion |
| Average daily extraction | $3.8 million |
| Sandwich attacks (2024) | 2.1+ million transactions |
| Front-running incidents | 850,000+ transactions |
How TEE Isolation Solves MEV
- Traditional MEV requires: (1) Seeing pending transactions, (2) Analyzing profitability, (3) Inserting/reordering transactions
- TEE isolation breaks step 1: Validator operators cannot see inside the TEE
- If you can't see transactions, you can't front-run them
- Current solutions like Flashbots only redistribute MEV; TEE isolation eliminates it
2.2 The Institutional Blockchain Gap
Bitcoin ETFs attracted over $115 billion in institutional inflows. 86% of institutional investors plan digital asset allocation—yet most cite infrastructure concerns. Institutions require verifiable execution, MEV protection, regulatory compliance, and operator accountability.
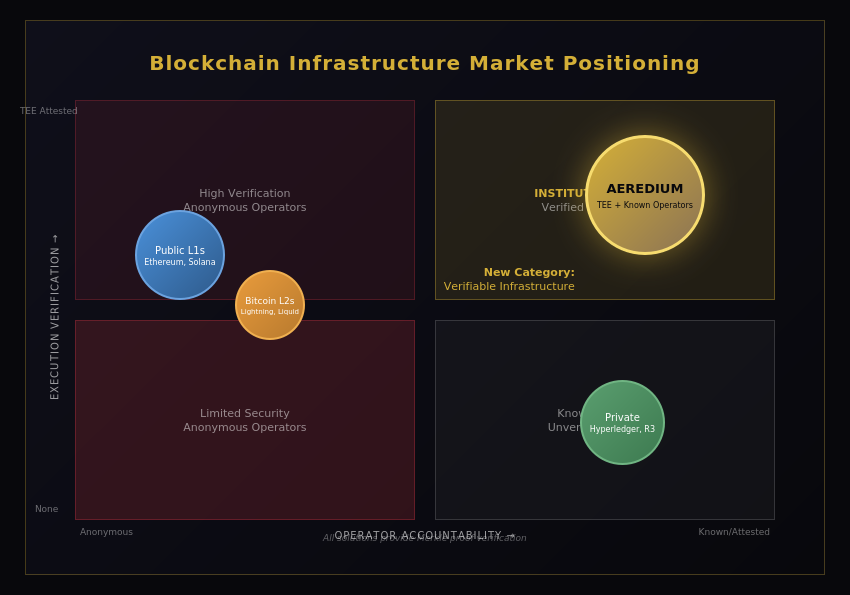
Figure 1: Blockchain Infrastructure Market Positioning
2.3 The Accountability Problem
When institutions ask "who operates your validators?" the answer for most blockchains is "we don't know." Merkle proofs verify state but not who computed it or what software ran.
Three Layers of Verification
- Merkle Proofs: Cryptographically verify WHAT the state is (all blockchains have this)
- TEE Attestation: Cryptographically verify WHERE code ran (hardware-isolated environment)
- ZK-STARKs: Cryptographically verify THAT computation was correct (quantum-resistant, no trusted setup)

Figure 2: Layered Security Model
3. Technical Architecture
3.1 Architecture Overview
AEREDIUM is an independent Layer 1 blockchain with a four-layer architecture optimized for institutional deployment and practical performance.
Transaction Flow
- Submission: Client submits standard EVM transaction with ECDSA signature (identical to Ethereum)
- TEE Reception: Transaction received by validator running inside TEE—operator cannot see contents
- Consensus: TEE-BFT orders transactions (first-come-first-served within TEE)
- Execution: Each validator executes within its hardware-isolated TEE
- ZK-STARK Attestation: Execution proof generated using ZK-STARKs (batched per block)
- Bitcoin Anchoring: ZK-STARK proofs committed to Bitcoin every 100 blocks
Layer Structure
| Layer | Description |
|---|---|
| Consensus Layer | TEE-BFT consensus for transaction ordering within TEEs |
| Execution Layer | Parallel EVM (Block-STM) within TEEs with standard Solidity support |
| Attestation Layer | ZK-STARK proofs for quantum-resistant execution verification |
| Anchoring Layer | ZK-STARK proofs + state roots committed to Bitcoin via OP_RETURN |
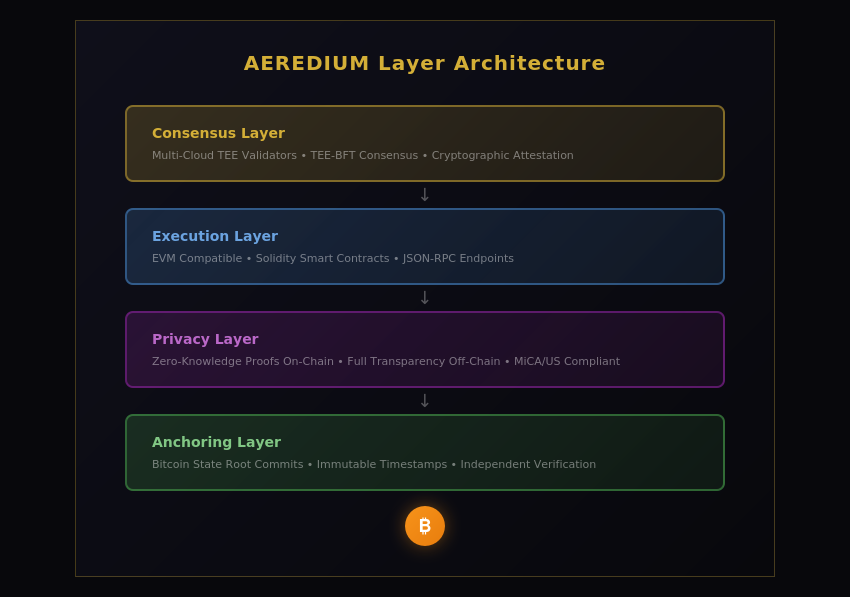
Figure 3: AEREDIUM Layer Architecture
3.2 TEE-Based MEV Protection
AEREDIUM achieves MEV protection through hardware isolation. This approach provides security with optimal performance and full EVM compatibility.
| MEV Attack | Requirement | TEE Protection |
|---|---|---|
| Front-running | See pending tx before inclusion | Operator cannot see inside TEE |
| Sandwich attack | Position txs around target | Cannot identify target tx |
| Transaction reordering | Modify tx sequence for profit | FCFS enforced inside TEE |
| Time-bandit attack | Reorg to capture past MEV | Bitcoin anchoring detects |
3.3 ZK-STARK Attestation Layer
AEREDIUM uses ZK-STARKs for execution attestation, providing quantum-resistant proofs without trusted setup requirements.
Why ZK-STARKs
| Property | zk-SNARK | zk-STARK |
|---|---|---|
| Proof Size | 288-384 bytes | 40-50 KB |
| Quantum Resistant | No (elliptic curves) | Yes (hash-based) |
| Trusted Setup | Required | Not required |
| Transparency | CRS required | Fully transparent |
3.4 Multi-Cloud Validator Network
The foundation of AEREDIUM's security is hardware-isolated Trusted Execution Environments (TEEs) deployed across three major cloud providers: AWS Nitro Enclaves, Azure SEV-SNP, and GCP Confidential Space.
Cloud Allocation Policy
| Cloud Provider | Target Allocation | Constraint Range |
|---|---|---|
| AWS Nitro Enclaves | 50% | 10% – 60% |
| Azure SEV-SNP | 30% | 10% – 60% |
| GCP Confidential Space | 20% | 10% – 60% |
These constraints are protocol-enforced: no single cloud can exceed 60% or fall below 10% of total validator capacity.
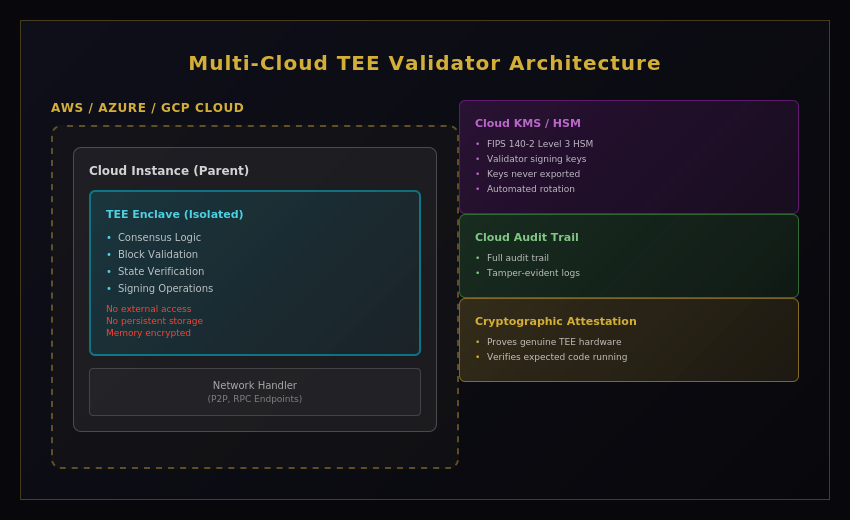
Figure 4: Multi-Cloud TEE Validator Architecture
3.5 TEE-BFT Consensus Mechanism
AEREDIUM employs TEE-BFT, a TEE-enhanced BFT consensus achieving 1-2 second finality with 2f+1 fault tolerance (reduced from 3f+1 through hardware attestation).
- Linear Message Complexity: O(n) instead of O(n²)
- Pipelined Phases: Overlapping prepare/pre-commit/commit maximize throughput
- TEE-Enhanced: 2f+1 threshold due to hardware-enforced non-equivocation
- 3-Chain Commit Rule: Finality in 3 rounds with proven safety
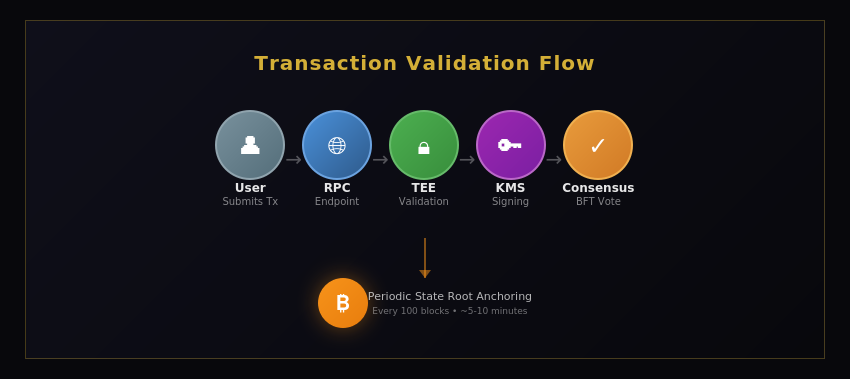
Figure 5: Transaction Validation Flow
3.6 Parallel EVM Execution Layer
AEREDIUM implements Block-STM style optimistic parallel transaction execution within TEEs. Result: 10,000+ TPS with full EVM compatibility.
Parallel Execution Model (Block-STM)
- Block with 1000 transactions distributed across parallel threads
- Thread 1: Tx 1-250 | Thread 2: Tx 251-500 | Thread 3: Tx 501-750 | Thread 4: Tx 751-1000
- Conflict Detection Layer identifies read/write conflicts
- Re-execute conflicting transactions only (<5% typical)
- Result: 10x-50x throughput improvement
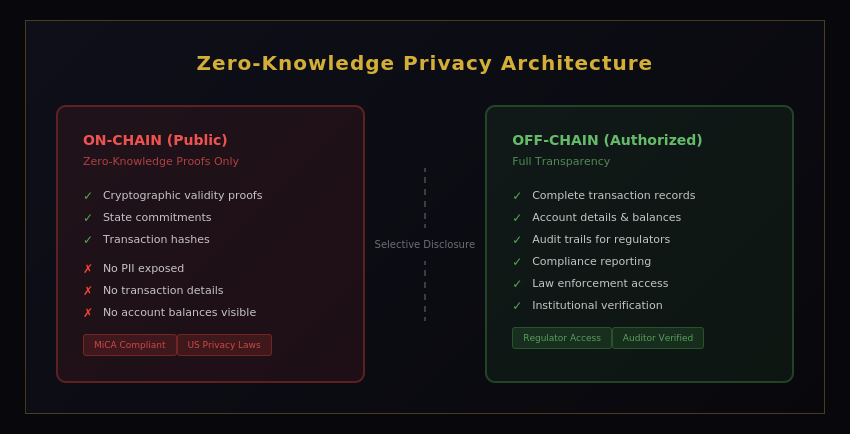
Figure 6: Zero-Knowledge Privacy Architecture
3.7 Bitcoin Anchoring
AEREDIUM periodically commits attestation proofs and state root hashes to the Bitcoin blockchain, creating an immutable audit trail.
- Frequency: Every 100 blocks (~5-10 minutes)
- Content: Merkle root of ZK-STARK proofs + state root for the block range
- Method: OP_RETURN: [STBL][version][proof_merkle_root][state_root][block_range]
- Cost: ~$1-5 per anchor at typical fee rates
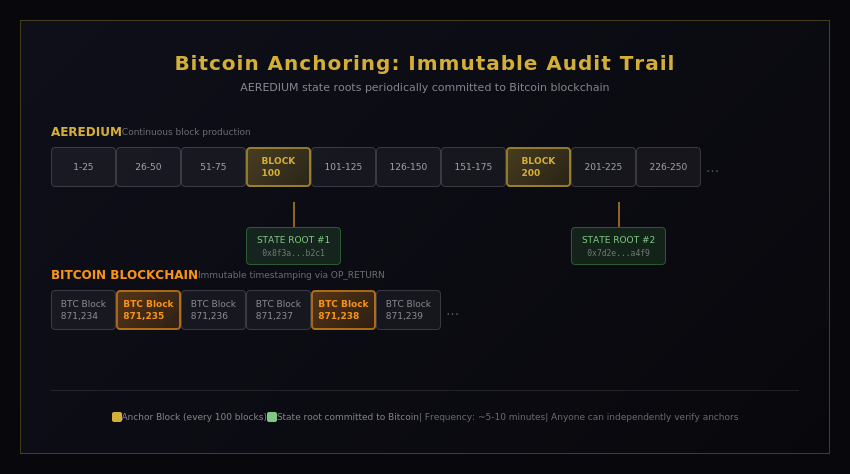
Figure 7: Bitcoin Anchoring - Immutable Audit Trail
3.8 Native Bridgeless Cross-Chain Interoperability
AEREDIUM integrates Kima Network's bridgeless cross-chain infrastructure directly into the execution layer. Every smart contract deployed on AEREDIUM automatically gains interoperability with 13 major blockchain networks.
Supported Networks: Bitcoin, Ethereum, Solana, Tron, Arbitrum, Optimism, Base, Polygon, BNB Chain, Avalanche, TON, Cosmos, and additional networks.
4. AER Native Token
AEREDIUM utilizes a native token called AER (AEREDIUM Token) for transaction gas fees. All operations on the network, including smart contract execution, token transfers, and state changes, require AER for gas payment.
The gas fee model ensures network sustainability while preventing spam and denial-of-service attacks. Gas fees are paid exclusively in AER, creating native demand proportional to network usage.
Detailed tokenomics, including total supply, distribution schedule, staking mechanisms, and governance rights, will be published in a separate Tokenomics White Paper prior to the token generation event.
5. Governance Framework
Governance is enforced programmatically. No human intervention is possible in consensus or execution.
Governance-controlled parameters: approved code hashes, cloud allocation targets, Bitcoin anchoring frequency, ZK-STARK proving parameters.
6. Security Model
6.1 Defense in Depth
Multiple independent security layers—compromise of one doesn't compromise the system:
| Security Layer | Protection Provided |
|---|---|
| TEE Isolation | Hardware prevents operator access to mempool/execution state (MEV protection) |
| ZK-STARK Proofs | Quantum-resistant mathematical proof of correct execution |
| Merkle Proofs | Standard blockchain state verification |
| Multi-Cloud | No single cloud provider can compromise network |
| Bitcoin Anchoring | Immutable timestamp of attestation proofs |
| BFT Consensus | 2f+1 fault tolerance with TEE enhancement |
| Cloud HSM | FIPS 140-2 Level 3 certified key storage |
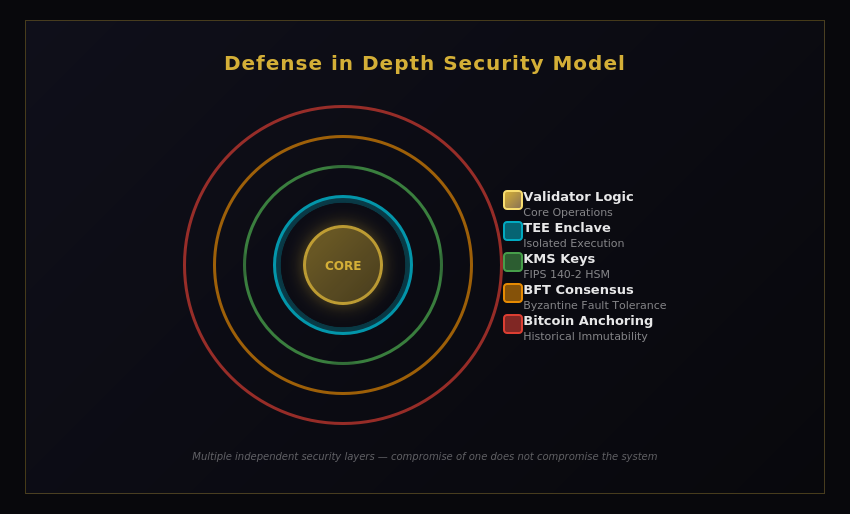
Figure 8: Defense in Depth Security Model
6.2 Security Comparison
| Platform | MEV Prot. | Quantum* | TEE | Operator | Bitcoin |
|---|---|---|---|---|---|
| AEREDIUM | ✓ TEE | ✓ STARK | ✓ Yes | ✓ Known | ✓ Anchor |
| Public L1s | ✗ None | ✗ No | ✗ No | ✗ Anon | ✗ No |
| Flashbots | ~ Redistr. | ✗ No | ✗ No | ~ Semi | ✗ No |
| Private Chains | ~ Partial | ✗ No | ✗ No | ✓ Known | ✗ No |
*Quantum resistance at attestation layer; user transactions use standard ECDSA with future migration path
7. Roadmap
Phase 1: Network Launch
- TEE-based validator network across AWS, Azure, GCP
- Standard EVM with ECDSA transactions
- ZK-STARK attestation layer
- Bitcoin anchoring
Phase 2: Ecosystem Growth
- Cross-chain bridges (Ethereum, Bitcoin)
- Observability dashboard
- Validator performance metrics
Phase 3: Advanced Features
- Privacy-preserving transactions via ZK proofs
- Dynamic cloud optimization
- Post-quantum user transaction signatures (as ecosystem matures)
- Advanced DeFi primitives
8. Conclusion
AEREDIUM delivers a production-ready blockchain architecture that achieves institutional-grade security without sacrificing EVM compatibility or performance:
- MEV protection through TEE hardware isolation
- Full EVM compatibility (standard ECDSA, standard addresses, standard tooling)
- Quantum-resistant attestation layer (ZK-STARKs)
- Multi-cloud validator diversity (AWS, Azure, GCP)
- Bitcoin-anchored audit trail
- Known, accountable operators with institutional compliance
The architecture leverages TEE hardware isolation to achieve MEV protection—if validators cannot see the mempool, they cannot extract value from transaction ordering. Quantum resistance is implemented at the attestation layer using ZK-STARKs, protecting execution integrity proofs while maintaining full compatibility with the existing EVM ecosystem.
AEREDIUM is positioned to become the trusted foundation for institutional digital asset operations—practical, performant, and prepared for the future.